Samuel Groß
@5aelo
V8 Security technical lead. Previously Project Zero. Personal account. Also @[email protected]
ID:1452156612
http://www.phrack.org/author_saelo.html 23-05-2013 18:20:02
709 Tweets
23,3K Followers
495 Following



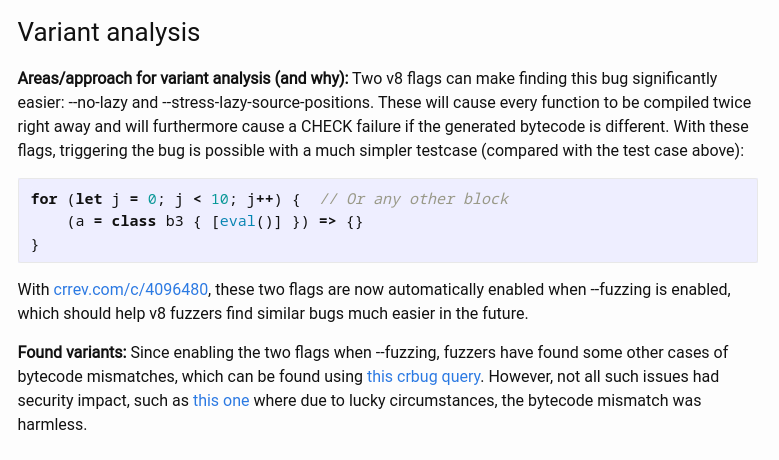
💫New RCA from Samuel Groß on CVE-2022-3723, a logic issue in Chrome's Turbofan JIT compiler.
googleprojectzero.github.io/0days-in-the-w…

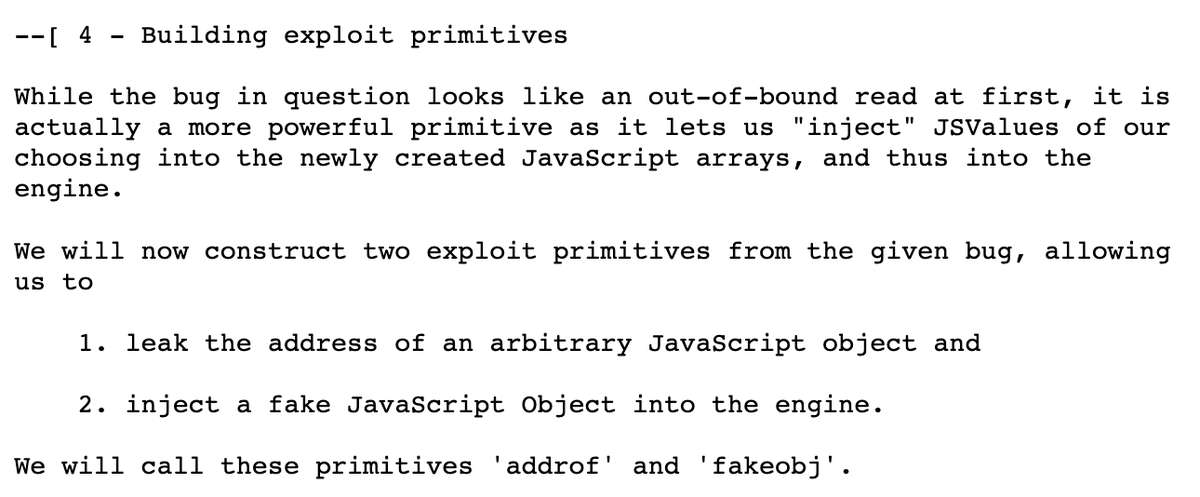
These #Phrack articles by Samuel Groß are the best primers on attacking #JavaScript engines
A case study of JavaScriptCore and CVE-2016-4622
phrack.org/issues/70/3.ht…
#Exploiting Logic #Bugs in JavaScript JIT Engines
phrack.org/issues/70/9.ht…

Fuzzilli (github.com/googleprojectz…), the great coverage-guided fuzzer for dynamic language interpreters based on a custom intermediate language built by Samuel Groß, is finally documented in a paper. You can find the paper at ndss-symposium.org/ndss-paper/fuz…




Some fun bugs found by Fuzzilli's new ProbingMutator (github.com/googleprojectz…):
- bugs.chromium.org/p/chromium/iss…
- bugzilla.mozilla.org/show_bug.cgi?i…
While these particular bugs don't have security impact, it's nice to see that Fuzzilli can now find these 2016-era JS engine bugs fairly easily.