PortSwigger Research
@PortSwiggerRes
Web security research from the team at @PortSwigger
ID:1177545689460592640
https://portswigger.net/research 27-09-2019 11:29:18
886 Tweets
87,2K Followers
7 Following
Follow People


There's still a load of potential for further research and discoveries in HTTP request smuggling. This massive-impact finding from I am d3d (dead, мёртв, 死了) exploiting Akamai/F5 is a great example:
blog.malicious.group/from-akamai-to…





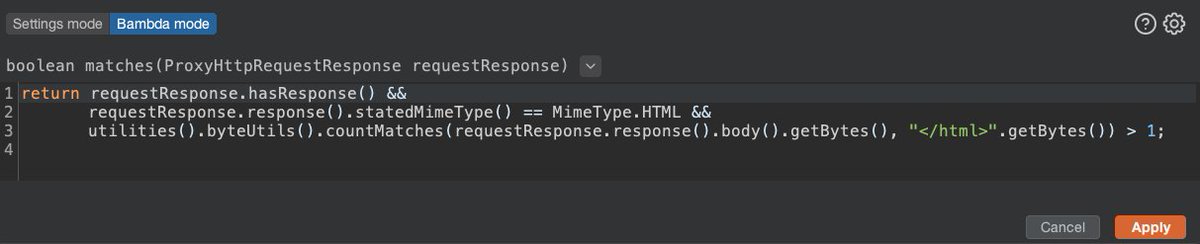
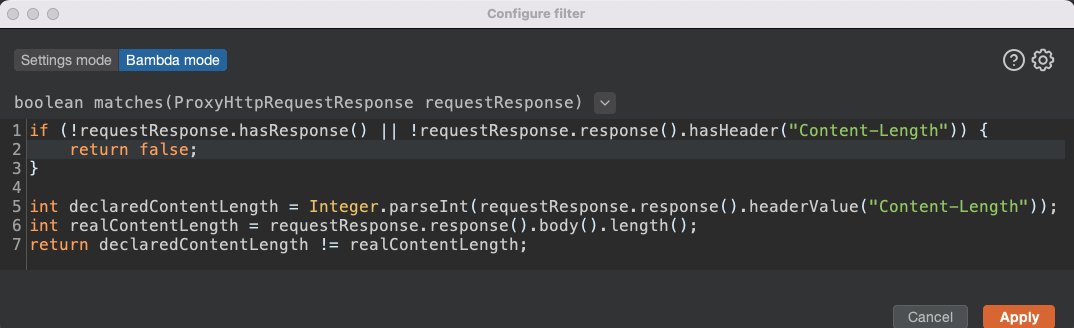
The new 'Bambda' feature that just landed in Burp Suite 2023.10.3 early-adopter is crazy powerful.
I just filtered through 250,000 requests in my proxy history to find ~70 with an incorrect response Content-Length!


We've just published 'How to build custom scanners for web security automation', using a recent dive into automated race-condition detection by James Kettle as a case study. Enjoy!
portswigger.net/research/how-t…





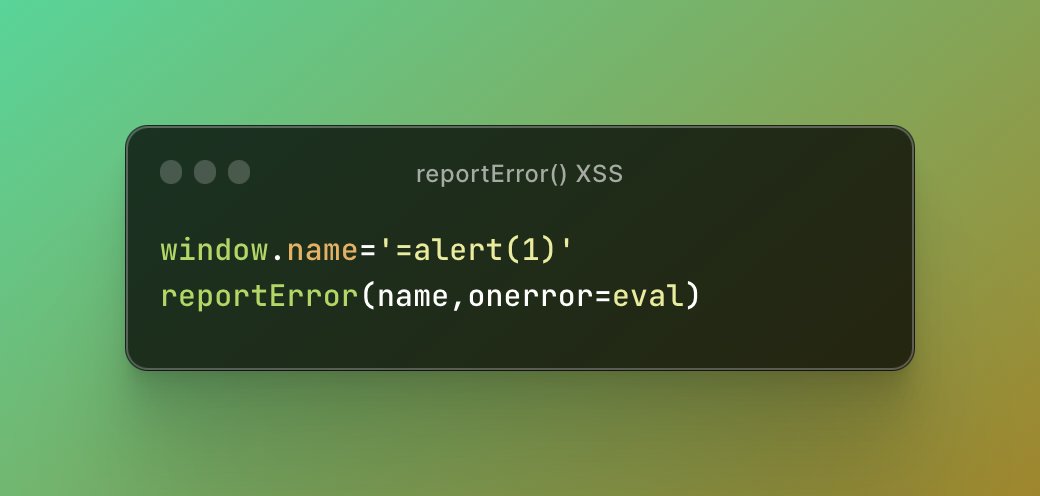
Have you found XSS inside a function call but severely restricted and can't use the characters `, (), ?, [], or ,? After a discussion on Twitter, Mathias Karlsson Frans Rosén found ways of getting around that restriction. We've updated our cheat sheet:
portswigger.net/web-security/c…



Burp Suite 2023.10 is harder to fingerprint than earlier versions as it now sets 'Accept-Encoding: gzip, deflate, br'. If you're still blocked, you might bypass it by tinkering with your TLS ciphers using 'Network->TLS -> Use custom protocols and ciphers'
portswigger.net/burp/documenta…

About Burp Suite and your RAM...
Over time, Java deliberately uses all the RAM you feed it, in order to minimise CPU cycles spent freeing memory. To feed it less memory, you can use the -XX:MaxRAMPercentage argument. For other RAM tips see:
portswigger.net/burp/documenta…